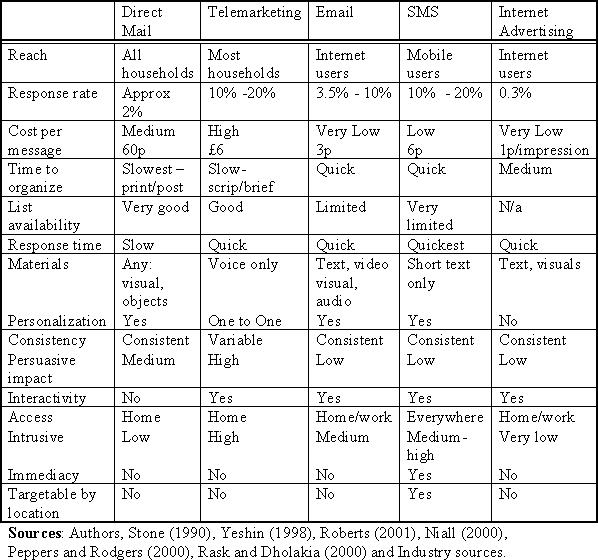
Table 1 Comparison of Direct and Internet Marketing Technique
Bulk Email Marketing
The advantages of email marketing have been recognised by a number of authors. Jackson and DeCormier (1999) recognised that email provided marketers with communication that permitted relationship building and real-time interaction with customers. Wreden (1999, p3) described email marketing as the 'Internet's killer application' because of the precision with which email can be tailored, targeted and tracked. Low costs and digital processing allows companies to send out huge numbers of emails. The medium is push rather than pull, the consumer does not have to instigate the interaction, and currently response rates are high (Di Ianni 2000; Rosenspan 2000). Peppers and Rodgers (2000, p 4), claim that 'clear benefits, including high response rates and low costs are rapidly turning email marketing into an invaluable tool'. Email marketing can be used for acquisition or retention; this paper focuses on acquisition email marketing, marketing designed to win rather than retain customers.
Table 1 Comparison of Direct and Internet Marketing Techniques
Table 1 compares email to other forms of direct and Internet marketing. The basic characteristics of email marketing are low costs, shorter turnaround (in the time involved to prepare, send the messages and receive the responses), high response rates and customisable campaigns. The advent of HTML, audio and video email improves the scope for creativity in email marketing. Ultimately it is conversion, rather than response rate, that will determine the cost efficiency of acquisition email marketing; this will depend on the targeting, the message, and the receptivity of the recipient. Briggs and Stipp (2000) have argued that the 'lean-forward' nature of the Internet increases involvement in streamed Internet advertising, this could equally apply to email marketing.
Email is a relatively new medium, in the future, consumer response is likely to be adversely affected by increasing traffic volume (Rosenspan 2000; Di Ianni 2000). Mehta and Sividas (1995) suggest that spam messages are unwanted, untargeted and therefore negatively perceived. Turban et al, (2000, p360) define spam 'as the practice of indiscriminate distribution of messages without permission of the receiver and without consideration for the messages' appropriateness.' Jupiter Communications (2000) estimate that the average US surfer will receive up to 1,600 unsolicited emails every year by 2005. Windham (2000) believes that unsolicited email is considered an invasion of privacy, and has already become a serious problem for some customers; spam taints the reputation of email marketing. To avoid being perceived as spam, several authors recommend that companies should restrict the messages they send (Wreden 1999; Wright and Bolfing 2001); in addition, marketers should obtain recipients' permission.
Permission Marketing
Godin, (1999, p 43) coined the term 'permission marketing' which is based on consumers giving their consent to receive marketing information. Permission marketing 'offers the consumer an opportunity to volunteer to be marketed to' and it is therefore 'anticipated, personal, and relevant'. The idea of consent is not new; customer permission had been introduced in the context of privacy issues in direct marketing (Milne and Gordon 1993). The key to permission marketing is knowing customer interests and knowing their information needs (Sterne and Priore 2000). It is particularly relevant to Internet marketing because the low marginal cost of messages creates a potential volume problem for both consumers and marketers. Permission marketing improves the targeting and relevance of promotional messages, thus improving response and conversion rates. The interactivity of the Internet facilitates communication of consumer permission and preferences.
A survey by IMT Strategies (1999) found that permission email has a higher response rate than non-permission email; more than half of their respondents felt positive about receiving permission email. Successful permission marketing is about building long-term relationships with customers once the initial permission has been granted. The consent, trust and two-way exchange of information develop the relationship between the consumer and the company.
Hagel and Singer, (1999) discuss the emergence of 'infomediaries' or information brokers who elicit the permission of consumers and preserve their privacy. In effect, these companies are 'permission' brokers; an example is yesmail.com.
Krishnamurthy (2001) presents a model where consumer interest in a permission-marketing program depends on five factors: message relevance; monetary benefit; personal information entry costs; message processing costs, and privacy costs. He also introduces the concept of permission intensity, which he defines as 'the degree to which a consumer empowers a marketer in the context of a communicative relationship'. In addition the permission may be more or less explicit. In-order to obtain as many permission email addresses as possible marketers sometimes provide options that are unclear with a default 'opt-in'. A study by Cyber Dialogue found that 69% of US Internet users did not know they had given their consent to inclusion on email distribution lists (Bellman et al 2001).
The effectiveness of direct marketing depends on the targeting, the nature of the offer, the creative, the timing and the volume of communication (Fraser-Robinson 1989; Stone 1996; Roberts and Berger 1989). Vriens et al., (1998, page 325) develop a theoretical framework for the response process in direct mail, see Figure 1, distinguishing between factors that affect the three stages: opening the envelope, paying attention to the contents and the response. |

